Three patches. That is the hard evidence.
One sat in FreeBSD for 17 years, a remote root exploit that nobody caught. Another lived inside OpenBSD since 1999, crashing machines through malformed TCP packets. A third hid in FFmpeg's H.264 decoder for 16 years while every fuzzer pointed at it missed. On April 7, Anthropic launched Project Glasswing, a gated coalition of AWS, Apple, Google, Microsoft, CrowdStrike, and roughly 40 other organizations. At its center sits Claude Mythos Preview, a model the company says has discovered "thousands of high-severity vulnerabilities" in every major operating system and web browser.
Three patches against thousands of claims. The gap between those numbers is where Anthropic's credibility now lives.
In an industry that has spent the past two years inflating benchmark scores, massaging evaluation results, and shipping models that fell apart under basic scrutiny, the default posture should be skepticism. Not cynicism. Skepticism. The kind that says: show me the CVEs, not the benchmark chart. Anthropic is asking the cybersecurity industry, the U.S. government, and eventually public market investors to trust that its unreleased model is as transformative as advertised. That ask arrives at the worst possible moment for trust in AI companies.
And the name? It lands differently once you know. Mythos, from the Greek, means speech. Tale. Story. That tracks. Right now, story is precisely what 99% of Anthropic's claims amount to. The patches are facts. The rest is a story waiting for verification.
Key Takeaways
- Four confirmed patches in FreeBSD, OpenBSD, FFmpeg, and Botan prove Mythos can find real, decades-old bugs in hardened code
- Over 99% of Anthropic's claimed "thousands" of discoveries remain unverifiable behind SHA-3 hashes until mid-2026
- Project Glasswing concentrates cybersecurity power in a gated Big Tech coalition with no independent governance
- The timing aligns with Anthropic's $380 billion valuation and potential October 2026 Nasdaq IPO
AI-generated summary, reviewed by an editor. More on our AI guidelines.
Four fixes prove the capability. The other 99% prove nothing yet.
The evidence that does exist is striking on its own terms. FreeBSD's security advisory for CVE-2026-4747 credits "Nicholas Carlini using Claude, Anthropic" for a stack buffer overflow enabling unauthenticated remote root access. The vulnerability research firm Calif.io independently reproduced the exploit. OpenBSD's errata 025_sack patches a kernel crash triggered by malformed TCP packets, fixing code that independent developer Simon Willison traced back 27 years. FFmpeg accepted a patch for a heap buffer overflow in H.264 decoding that, according to Anthropic, survived 5 million automated fuzzer hits without detection. A fourth fix landed on the launch day itself: the Botan cryptography library patched a certificate verification bypass (CVE-2026-34580), crediting "Nicholas Carlini with Claude."
These are not toy demonstrations. They establish that Mythos can find deep, logic-level bugs in hardened codebases where decades of expert review and automated tooling came up empty.
But Anthropic's own Mythos post concedes that fewer than 1% of the vulnerabilities it has identified are patched so far. The remaining 99% sit behind SHA-3 cryptographic commitments, hashes the company published to prove it found the bugs first. The scheme is clever. It is also, by design, unverifiable until disclosure deadlines pass sometime between July and September 2026. CNN noted it "could not immediately verify" the thousands-of-vulnerabilities figure. The New York Times counseled readers to "take claims about unreleased model capabilities from A.I. companies with a grain of salt."
Then there is the internal validation. Anthropic reports that professional security contractors agreed with Mythos's severity assessments in 89% of 198 manually reviewed reports. Strong numbers. But those contractors were hired and paid by Anthropic. No external audit of the validation pipeline has been published. The severity-agreement metric is self-reported, based on a sampling methodology Anthropic controls. Independent review would look different. It does not exist.
Aikido Security offers a useful counterweight. The testing company ran 1,000 real-world AI penetration tests and found that whitebox conditions, where the model has full source code access, produced seven times more findings than greybox tests simulating real attacker conditions. Defenders hold a structural advantage that the "doomsday framing" obscures. "The balance hasn't tipped," Aikido concluded. That does not mean Mythos is overhyped, though that distinction is almost beside the point. It means context matters more than headline numbers, and context is exactly what Anthropic's marketing omits.
A butterfly named for transparency that nobody can see through
Project Glasswing borrows its name from the glasswing butterfly, whose transparent wings signal openness. The metaphor collapses on contact with the program's actual governance.
Glasswing's 12 launch partners include every major cloud provider, the largest cybersecurity vendors, and JPMorgan Chase. Anthropic committed $100 million in usage credits and $4 million in donations to open-source security organizations. Partners must share findings with the broader industry. Anthropic pledged a public report within 90 days. All of this sounds responsible.
What Glasswing does not have is any independent governing authority. Anthropic decides who gets access. The company's blog post gestures toward a future "independent, third-party body" for large-scale cybersecurity projects, but frames this as aspirational. No timeline. No charter. No teeth. The model's operator is also its creator, the coalition's convener, and the entity briefing CISA and the Commerce Department on offensive capabilities. Kelsey Piper, the Vox reporter who covers AI safety and has broken several stories on Anthropic's internal deliberations, put it bluntly: "A private company now has incredibly powerful zero-day exploits of almost every software project you've heard of."
CrowdStrike's CTO Elia Zaitsev told the New York Times the model represents "a significant cybersecurity risk." Yet CrowdStrike's published governance position is that "model safety is the builder's responsibility" while "deployment governance is ours." That framework conveniently places Anthropic in charge of what Mythos does and CrowdStrike in charge of selling protection against it. The partners are not referees. They are customers who became distribution channels, positioning themselves as coalition members rather than competitors caught flat-footed by a model that threatened to eat their market.
Google's Project Zero and the DARPA Cyber Grand Challenge both operated without this kind of corporate intermediation. Glasswing borrows their disclosure norms and adds a layer of gatekeeping that neither had. Casey Newton at Platformer articulated the deeper tension: "Glasswing is built on a deeply uncomfortable premise, that the only way to protect us from dangerous AI models is to build them first."
Get the analysis that cuts through AI hype
Strategic AI news from San Francisco. No hype, no "AI will change everything" throat clearing. Just what moved, who won, and why it matters. Daily at 6am PST.
No spam. Unsubscribe anytime.
The IPO that needs a safety narrative
Strip away the national security language and the commercial logic is plain.
After the subsidized preview, Mythos Preview will cost $25 per million input tokens. Partners pay once credits run out. A Cyber Verification Program is planned for ongoing professional access. This is enterprise SaaS, land-and-expand, with "$100 million in free credits" as the wedge.
Anthropic's annualized revenue hit $30 billion as of the announcement, up from roughly $9 billion at the end of 2025. The company's valuation reached $380 billion in its February 2026 funding round. Bloomberg and multiple outlets report that Anthropic is evaluating a Nasdaq IPO as early as October 2026, potentially raising over $60 billion.
The math writes itself. VentureBeat noted dryly that "a high-profile, government-adjacent cybersecurity initiative with blue-chip partners is exactly the kind of program that burnishes an IPO narrative."
Cybersecurity stocks felt the signal before the coalition formed. After Fortune leaked Mythos's existence in March, CrowdStrike, Palo Alto Networks, Zscaler, SentinelOne, Okta, and Tenable fell 5 to 11%. They partially recovered when those same companies appeared as Glasswing partners, co-opted from potential disruption victims into API customers. If you run a security vendor, Glasswing gives you a choice: compete against Mythos or integrate it. Most chose integration. That is the moat.
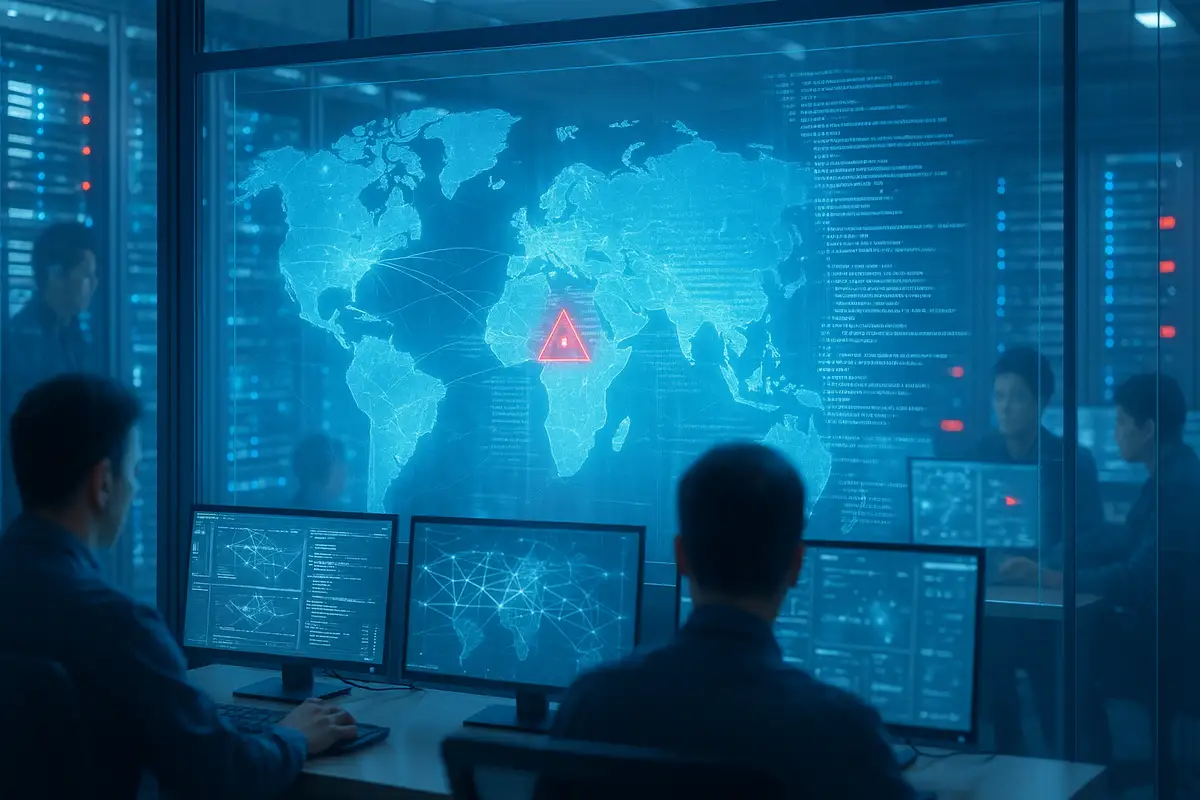
And it is a moat with a countdown timer. Logan Graham, head of Anthropic's frontier red team, told Axios that rival labs are 6 to 18 months from comparable capabilities. Google DeepMind's Big Sleep project has already confirmed over 25 zero-day vulnerabilities since November 2024. OpenAI's Codex Security, launched the same month, already has 14 CVEs to its name after just 30 days of scanning. Anthropic acts emboldened by its head start. The head start is shrinking. Every month that passes without a steady stream of public patches and CVEs makes the Glasswing narrative harder to sustain.
The company that couldn't secure its own CMS
There is an irony here that should make any observer anxious.
Mythos's existence was revealed in March through a misconfigured content management system that left nearly 3,000 unpublished assets publicly searchable. Weeks earlier, Anthropic accidentally exposed over 2,000 source code files and 500,000 lines of Claude Code through a packaging error, then caused roughly 8,100 GitHub repositories to be taken down while trying to clean up via DMCA notices. A company that wants to guard the internet's code could not keep its own blog drafts off the public web.
Gizmodo went further back. Remember GPT-2? OpenAI called it "too dangerous to release" in 2019. Shipped it months later anyway. It could not reliably count the letter "r" in "strawberry." The script has not changed much: flag the threat, control who touches it, build a business around the fix. What is different this time is that three real patches suggest the danger might actually be real. Which makes the governance gap more concerning, not less.
The Pentagon standoff adds another layer. Defense Secretary Pete Hegseth designated Anthropic a "supply chain risk" after the company refused to remove guardrails against domestic mass surveillance and lethal autonomous weapons. A federal judge blocked that designation in March, calling it "classic illegal First Amendment retaliation." But the label, even temporarily, signals how fragile Anthropic's institutional position remains. You cannot simultaneously be the industry's cybersecurity savior and a designated threat to national security. One of those stories has to give.
Trust is not a hash commitment
The SHA-3 hashes will start resolving between July and September 2026. If the disclosed vulnerabilities match the severity and scope Anthropic has claimed, the company will have earned something genuinely rare in this industry: verified credibility at scale. If the disclosures underwhelm, the $100 million Glasswing investment becomes the most expensive marketing campaign in cybersecurity history.
Until then, the industry is being asked to believe, not verify. In a year that has already produced inflated benchmarks, leaked capabilities deployed for attention, and press releases confused with peer review, that ask carries weight it should not have to.
Three patches are real. The name, at least, is honest. Mythos means story. And a story is exactly what 99% of these claims remain.
Frequently Asked Questions
What is Claude Mythos Preview?
Claude Mythos Preview is Anthropic's most advanced AI model, built for autonomous vulnerability discovery. It scores 83.1% on Anthropic's CyberGym benchmark versus 66.6% for the prior Opus 4.6. Anthropic says it found thousands of security flaws but will not release the model publicly due to dual-use risks.
What vulnerabilities has Mythos actually confirmed?
Four publicly verified fixes exist: a 17-year-old remote root exploit in FreeBSD (CVE-2026-4747), a 27-year-old TCP flaw in OpenBSD, a 16-year-old heap overflow in FFmpeg, and a certificate verification bypass in Botan (CVE-2026-34580). All credit Anthropic researcher Nicholas Carlini using Claude.
What is Project Glasswing?
A gated cybersecurity coalition launched April 7, 2026. Partners include AWS, Apple, Google, Microsoft, CrowdStrike, and about 40 other organizations. Anthropic committed $100 million in usage credits and $4 million to open-source security groups. Partners get early Mythos access to patch vulnerabilities before similar capabilities spread.
Who governs Project Glasswing?
Anthropic alone. The coalition has no independent governing authority. Anthropic decides access and terms. The company mentions a future third-party body but with no timeline or charter. Critics note Anthropic simultaneously acts as model creator, coalition convener, and government briefer.
How does Glasswing connect to Anthropic's IPO plans?
Anthropic's revenue hit $30 billion and its valuation reached $380 billion. Bloomberg reports a potential Nasdaq IPO as early as October 2026. After the subsidized preview, Mythos costs $25 per million input tokens. VentureBeat called the government-adjacent initiative the kind of program that burnishes an IPO narrative.
AI-generated summary, reviewed by an editor. More on our AI guidelines.


 IMPLICATOR
IMPLICATOR